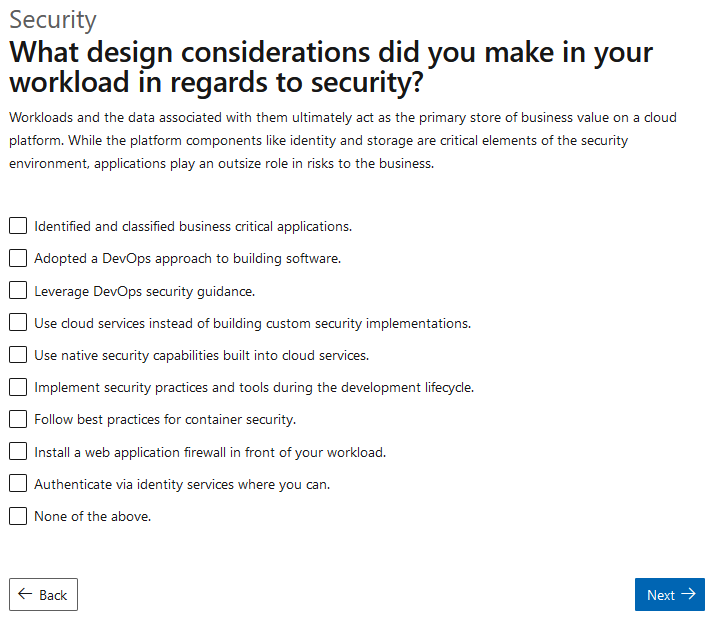
Azure Well-Architected - Security Question 1
Azure has finally released their Well-Architected documentation, which contains a wealth of knowledge on a range of topics as it relates to the cloud. As part of this release, they have also released a questionnaire. The goal of this post is to have a look at the first security question in the assessment.
You can find the assessment here.
I am honestly a fan of this question, although I think the options need a bit of work from an application perspective. When we start down a security track, the first objective to accomplish with clients is to establish security goals for the organization. The process involves bringing up various considerations (along the people, process, technology lines) that the company needs to pay attention to when driving their solutions. So this question is pretty fitting here. Lets go through a couple of the asks.
Ask 1: Identified and Classified business critical applications
When doing a top-down approach to security, this is usually step one for most organizations. Ultimately, you want to be able to justify why you are implementing a particular security control, since those controls require effort/money/time etc.
I think the interesting advice to consider here is that how much time you spend classifying your applications (and justifying controls) likely depends on the size of your organization. If you are a startup, your focus should likely be less on classification exercises, and more on defining security baselines for the app itself. In fact, one classifies applications solely to understand the security rigour that should be applied to said application.
If I were to redirect this ask, it would be more along the lines of designing security baselines taking into consideration the security landscape of the applications (or business) utilizing it.
Here are some resources to get you started:
https://docs.microsoft.com/en-us/learn/modules/create-security-baselines/
https://www.cisecurity.org/benchmark/azure/
https://docs.microsoft.com/en-us/azure/cloud-adoption-framework/govern/security-baseline/toolchain
Ask 2: Leverage DevOps Security Guidance
Saweet. Can I please take four orders of devops security guidance? Here’s my credit card!
I like to think that I’m a security professional (by day at least) and so I should likely know what they mean by “devops security guidance”. A google search yields ads (one of them for gartner, which I click on to further my eDOS attack) and a 2019 blog post from Microsoft.
I think a discussion of devops and security is beyond the scope of this post, suffice to say, if you are confused about exactly what they mean by this….. You are not alone.
Best I can tell, this checkbox is probably more around setting up appropriate security principles and then enforcing it with automation and continuous improvement. For some ideas, see https://docs.microsoft.com/en-us/azure/architecture/framework/security/security-principles
Other relevant links:
https://azsk.azurewebsites.net/
Ask 3: Use native security capabilities built into cloud services
I really like this question. Much like question 1, I think that one’s approach to securing the cloud can be placed on a continuum from small to large enterprises. When I engage with large enterprise security teams, they are typically routed in the past. Initially, their goals are to “extend” their existing security capabilities to the cloud. I feel that this approach is mostly taken from a position of comfort, rather than a practical decision on the effectiveness of alternate toolsets.
To start your journey, have a look at https://docs.microsoft.com/en-us/azure/security/fundamentals/security-controls
Conclusion
In conclusion, I think that these types of questions and assessments are a good thing, overall, for the cloud industry. It is important that while the cloud seems like something you just “turn on”, in reality, there is much more to it. Hopefully these types of assessments will lead to more organizations taking a conscious look at their cloud strategy up front.
About Shamir Charania

Shamir Charania, a seasoned cloud expert, possesses in-depth expertise in Amazon Web Services (AWS) and Microsoft Azure, complemented by his six-year tenure as a Microsoft MVP in Azure. At Keep Secure, Shamir provides strategic cloud guidance, with senior architecture-level decision-making to having the technical chops to back it all up. With a strong emphasis on cybersecurity, he develops robust global cloud strategies prioritizing data protection and resilience. Leveraging complexity theory, Shamir delivers innovative and elegant solutions to address complex requirements while driving business growth, positioning himself as a driving force in cloud transformation for organizations in the digital age.