
Cloudy With a Risk of Thunderbolts
USB has always been a security concern. A malicious device that has been plugged into a USB port could impersonate a phantom keyboard and log all your keystrokes. Another popular exploit was to make use of the Windows autorun feature and have a storage device deliver a software exploit payload. I could go on, but you have heard it all before.

Thunderbolt
The Thunderbolt 3 port is a recent addition to PCs. It looks identical to a USB 3.x Type-C port, which is also a recent addition. Other then a small Thunderbolt icon, there is no physical difference in the port.
The Thunderbolt port is a jack-of-all-ports that is extremely powerful, but that power needs to be controlled responsibly or it can become extremely dangerous. The standard combines direct PCI express bus access, DisplayPort (video), and USB 3.0 (peripherals) in an interface that borrows the same Type-C connector used by USB 3.x. Because it supports USB 3.x it is fully compatible with all USB devices and can easily be confused for a standard USB 3.x port.
The huge mess of confusion with the recent USB 3.x specifications and the borrowed USB Type-C port are really not helping consumers. The modern version of explaining to your parents how to program a VCR has become explaining the finer intricacies of choosing the right device, cable, hub, and port combination to achieve the fastest throughput or charging speed. A whole article could be written on explaining how to decipher the USB 3.0 specifications, manufacturer power workarounds, and rampant inaccurate labeling.
Question:
What throughput and charge rate could I expect when plugging in a USB 3.2 Gen 2x2 device using a USB 3.0 cable less than 1m long into a Thunderbolt 3 port?
Answer:
As long as the cable properly conforms to the USB 3.0 SuperSpeed standard, I am 86% certain that if we start with 2 lanes at 5Gbit/s and take into account the 8B/10B encoding with an additional 20% reduction from protocol overhead we would get 800MB/s at a possible charging power of 3 Amps at 5 volts or 15 Watts. Power could drop to 0.9 Amps or 4.5 Watts depending on how the cable responds to the USB controller. If the cable is a relabelled USB 2.0 cable, we would end up at pitiful 43MB/s of throughput and as low as 500mA or 2.5 watts of power.
…Back to the Topic
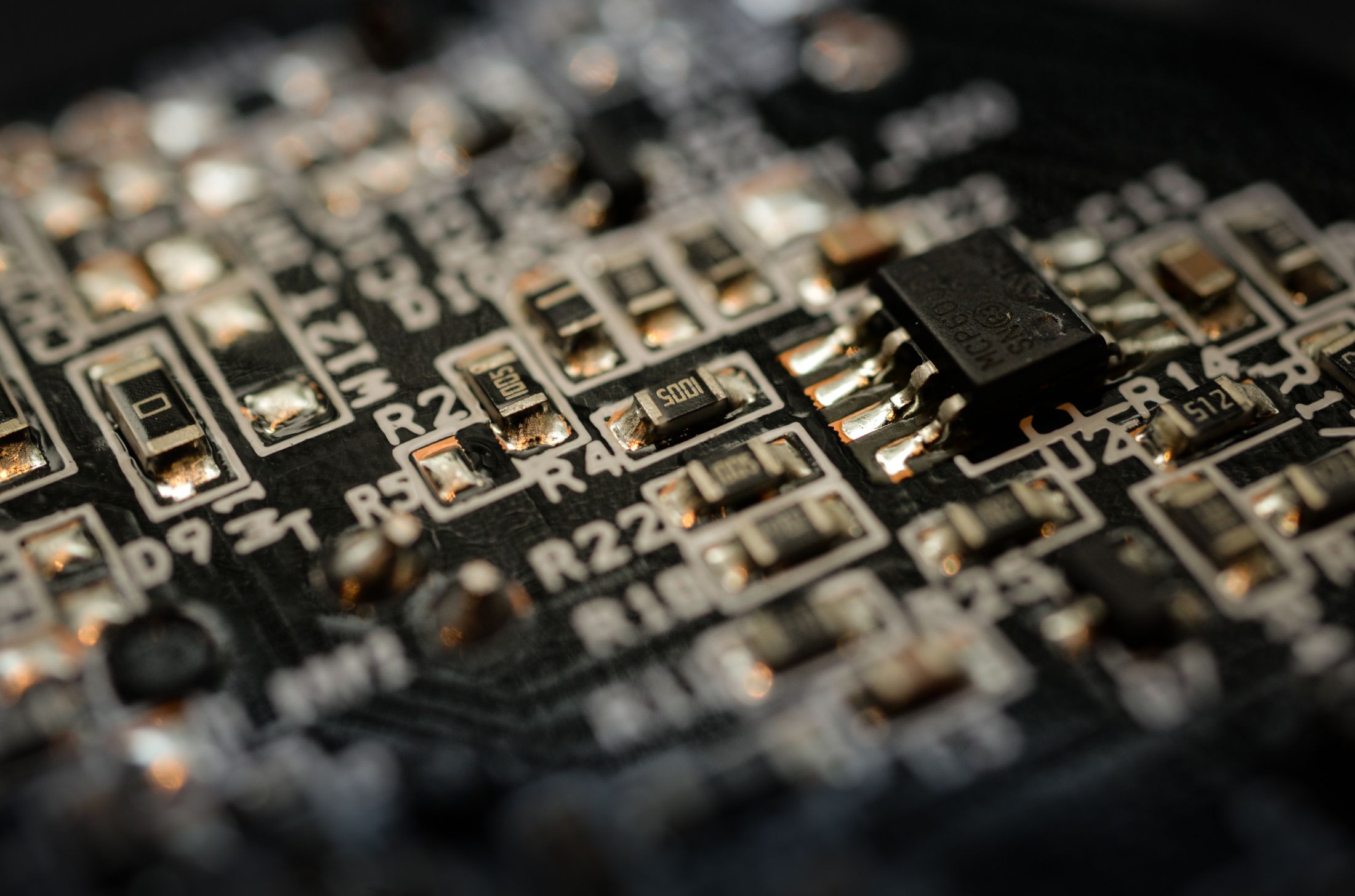
With the advent of Thunderbolt the attack surface has greatly been increased. External devices can now have direct access to the PCI express (PCIe) bus. This is the internal communication network of your computer. Sensitive data passes over this network between your processor, memory, video card, network card, and now connected external devices. It now is possible for a malicious device to monitor your network traffic, read sensitive data from memory or write malicious content to memory that can then be executed.
.jpg)
Am I Protected out of the Box?
There are protections in place, but they are mainly reliant on software.
The first line of defence is the Thunderbolt security level settings found in the BIOS. If it is left at the default, you will be protected until the operating system has been loaded. After that point it is up to the security of the operating system and driver to maintain protection.
If the BIOS setting is set to legacy mode, you will be fully exposed to any attached malicious device. Complete Thunderbolt support in Linux has only been recently added. Previously, setting the Security Level to legacy was the only way to get Thunderbolt devices to work fully under Linux.
http://blog.frizk.net/2016/10/dma-attacking-over-usb-c-and.html
A Round of Applause is in Order
The second line of defence, or should I say attack surface of the day, are the Input-Output Memory Management Units (IOMMUs). They allow the operating system to restrict access to your computer’s memory. Some operating systems by default don’t enabled this security feature due to performance reasons and if it is enabled, their implementation is full of holes. Within the last few days research has been disclosed that found all mainstream operating systems have vulnerabilities in how they handle Thunderbolt. The issues were discovered and reported to operating system vendors back in 2016 and still haven’t been fully patched.
Windows 10:
Version 1803 properly supports IOMMU, but some vulnerabilities remain.
MacOS:
Version 10.12.4 protects against one vulnerability, but other vulnerabilities remain.
Linux:
The unreleased kernel 5.0 is fully patched, but the stable 4.x releases are not.

You Can’t Trust Your Intel
The last line of defence is the software-based authorization supplied with the Intel Thunderbolt driver. The gatekeeper to your computer’s most sensitive data is an application controlled by one vendor, Intel. Intel has a poor track record when it comes to security. The Management Engine/Spectre fiasco is a prefect example. I wouldn’t be surprise if they also played a large part in the Thunderbolt and IOMMU implementations of the operating system vendors.

Users Are the Champions of Safety
If you have ever plugged in a Thunderbolt device, you will get a prompt asking you to approve the device at a requested security level. History has proven when a user is presented with a prompt requesting permission they sometimes approve the request without realizing what they are doing. If nothing immediately breaks, to continue on. I can see another round of parking lot USB Type-C key exploits making the rounds.
It is paramount that you fully trust what you plug into a Thunderbolt port.
Meet the new bus, same as the old bus.
About James MacGowan

James started out as a web developer with an interest in hardware and open sourced software development. He made the switch to IT infrastructure and spent many years with server virtualization, networking, storage, and domain management.
After exhausting all challenges and learning opportunities provided by traditional IT infrastructure and a desire to fully utilize his developer background, he made the switch to cloud computing.
For the last 3 years he has been dedicated to automating and providing secure cloud solutions on AWS and Azure for our clients.